Are you curious about what Zama is and how it’s shaping the future of blockchain technology? If you’ve ever wondered why public blockchains struggle with confidentiality, you’re not alone. Builders, businesses, and regulators all face the same tension between transparency and privacy, and that tension is driving growing attention toward encrypted computation and the ZAMA token that supports this emerging ecosystem.
In this article, you will learn about Zama’s unique approach to solving privacy challenges, its torus fully homomorphic encryption (FHE) technology, and how it powers applications like private stablecoins, confidential DeFi, and privacy-preserving AI. We’ll also explore the ZAMA token’s utility, its ecosystem, and how it compares to other privacy technologies. Ready to get into the details? Read on.
What Is Zama?
Zama is a privacy-focused blockchain infrastructure company building the Zama Network to make confidential computing possible on public blockchains. If you understand the blockchain basics, you already know that transparency is both a strength and a limitation. Zama works on the missing layer by letting encrypted smart contracts process encrypted data without exposing it on-chain.
Zama reached a major milestone by becoming the first company focused on fully homomorphic encryption to achieve unicorn status, following a funding round that brought in $57 million. It crossed a valuation above $1 billion in June 2025, becoming the first unicorn built entirely around fully homomorphic encryption. That milestone followed a strong Series B funding round backed by Pantera Capital, signaling serious confidence from institutional crypto investors.
Rather than creating a closed system, the Zama Network aims to plug into existing blockchains and developer workflows. This approach helps teams build confidential applications that keep balances, encrypted inputs, and logic private while staying decentralized and verifiable. Zama positions itself at the intersection of privacy, compliance, and real-world blockchain adoption.
What Problem Does Zama Solve?
Public blockchains expose customer data by design. Every balance, transaction detail, and smart contract input sits in plain view, which creates serious limits for real financial, enterprise, and institutional use. Users lose privacy, businesses cannot protect sensitive logic, and regulators struggle to support compliant systems built on fully transparent ledgers. This gap slows adoption and forces developers to choose between decentralization and confidentiality.
Zama’s technology addresses this problem by allowing smart contracts to compute directly on encrypted data. Instead of hiding activity off-chain or relying on trust assumptions, applications keep information confidential while still running on public networks. This approach protects user balances, transaction amounts, and business rules without breaking composability or auditability.
Without native confidentiality, many use cases simply do not work on-chain, including private payments, compliant identity systems, and enterprise data processing. Zama’s technology removes this barrier and makes it possible to build applications that respect privacy while staying decentralized, verifiable, and usable at scale.
How Does Zama Work?
Zama operates using fully homomorphic encryption (FHE), a groundbreaking method that allows encrypted values to be processed without decryption. This ensures that sensitive information remains secure throughout its entire lifecycle, even during computation.
The foundation of Zama’s technology lies in its core architecture, which includes programmable bootstrapping. This feature enables efficient and scalable encrypted computations, making it practical for real-world applications.
Encrypted data types in encrypted smart contracts further enhance privacy by allowing developers to build secure applications without exposing customer data. Threshold decryption is another key component, ensuring that only authorized parties can access decrypted results. This combination of advanced encryption techniques and blockchain integration makes Zama a powerful tool for industries requiring high levels of data confidentiality, such as finance, healthcare, and artificial intelligence.
Fully Homomorphic Encryption (FHE) Explained


Fully homomorphic encryption allows computations to run directly on encrypted values without exposing the original values at any point. For blockchain applications, this removes the need to reveal balances, inputs, or business logic just to execute a smart contract. The Zama Protocol uses FHE so applications can process sensitive information on public networks while keeping that data private by default. This foundation also opens the door for economic incentives, since secure computation creates new roles for validators and participants, which is where tokenomics may apply to Zama becomes relevant.
FHE alone is not enough to support real applications at scale. The confidentiality protocol must translate advanced cryptography into a system that developers can actually use, which leads directly into how Zama structures its core architecture.
Zama Core Architecture
The Zama Protocol combines FHE with blockchain execution to support smart contracts that operate entirely on encrypted data. Developers interact with familiar programming models, while the network handles encrypted computation, verification, and controlled decryption. This structure allows privacy to coexist with decentralization and composability, and it also creates clear points where incentives and protocol fees can align with network usage and security.
1. Programmable Bootstrapping
Programmable bootstrapping refreshes encrypted circuits values during computation so contracts can run complex logic without losing accuracy. Zama applies this technique to support conditional logic and repeated confidential operations inside smart contracts. As usage grows, this process becomes a measurable resource, which helps explain how tokenomics may apply to Zama through computation costs and network rewards.
2. Encrypted Data Types in Smart Contracts
Zama provides encrypted data types that behave like standard variables while keeping their contents hidden. Smart contracts can store, compare, and update these values without ever revealing them on-chain. This feature makes privacy native to application design and creates demand for secure execution, which can be priced and incentivized through the protocol’s economic model.
3. Threshold Decryption
Threshold decryption splits decryption authority across multiple participants so no single entity controls access to sensitive results. Only when a required group cooperates can the final output be revealed. This design strengthens security and supports decentralized trust, while also defining roles that may earn rewards, further showing how tokenomics may apply to Zama as the network matures.
Key Features of the Zama Protocol
As privacy moves from a nice-to-have to a real requirement, Zama focuses on building practical tools that developers and businesses can actually use. The confidential protocol does not treat confidentiality as an add-on. It builds it directly into how specialized smart contract engines execute and interact. Here are the key features that define the Zama Protocol and explain why it stands out.
1. Native Encrypted Computation
Zama allows smart contracts to compute directly on encrypted data. Encrypted inputs, states, and outputs remain confidential throughout execution. This design removes the need to reveal sensitive information just to use a decentralized application, while still preserving correctness and verifiability on-chain.
2. Open-Source Cryptographic Framework
The Zama Protocol follows an open source cryptography company model, giving developers and researchers full visibility into its cryptographic components. This approach encourages audits, community contributions, and long-term trust. By keeping the core technology open-source, Zama supports transparency at the protocol level while protecting user data at the application level.
3. Developer-Friendly Smart Contract Integration
Zama provides encrypted data types and tooling that fit into familiar smart contract workflows. Developers do not need to redesign applications from scratch to support privacy. They can build using established patterns while the protocol handles encrypted computation behind the scenes.
4. Decentralized and Secure Decryption
The Zama protocol operates on a threshold-based mechanism to control how and when encrypted results become readable. No single participant can decrypt sensitive data alone. This structure reduces trust assumptions and aligns with decentralized security principles.
5. Composability With Existing Blockchains
Zama designs its technology to work alongside existing blockchain networks rather than replacing them. Applications can remain interoperable while gaining compliant confidentiality, making it easier to integrate encrypted data into broader decentralized ecosystems.
Advantages and Limitations of Zama (FHE)
Zama’s fully homomorphic encryption (FHE) technology offers groundbreaking solutions for data privacy and security. However, like any technology, it comes with its own set of advantages and limitations.
Advantages of Zama (FHE)
Enhanced Data Privacy: Zama ensures that sensitive information remains encrypted throughout its lifecycle, eliminating the risk of exposure during processing.Versatility Across Industries: The protocol is adaptable to various sectors, including finance, healthcare, and artificial intelligence, where data confidentiality is critical.Open-Source Collaboration: Zama’s open-source framework fosters innovation and transparency, allowing developers to contribute and improve the technology.Scalability: The architecture supports efficient and scalable encrypted computations, making it practical for real-world applications.
Limitations of Zama (FHE)
Computational Overhead: Fully homomorphic encryption requires significant computational resources, which can impact performance in certain scenarios.Complexity for Developers: Implementing FHE-based solutions may require specialized knowledge, posing a learning curve for developers new to the technology.Adoption Challenges: As a relatively new technology, FHE may face resistance from industries unfamiliar with its benefits or hesitant to adopt advanced encryption methods.
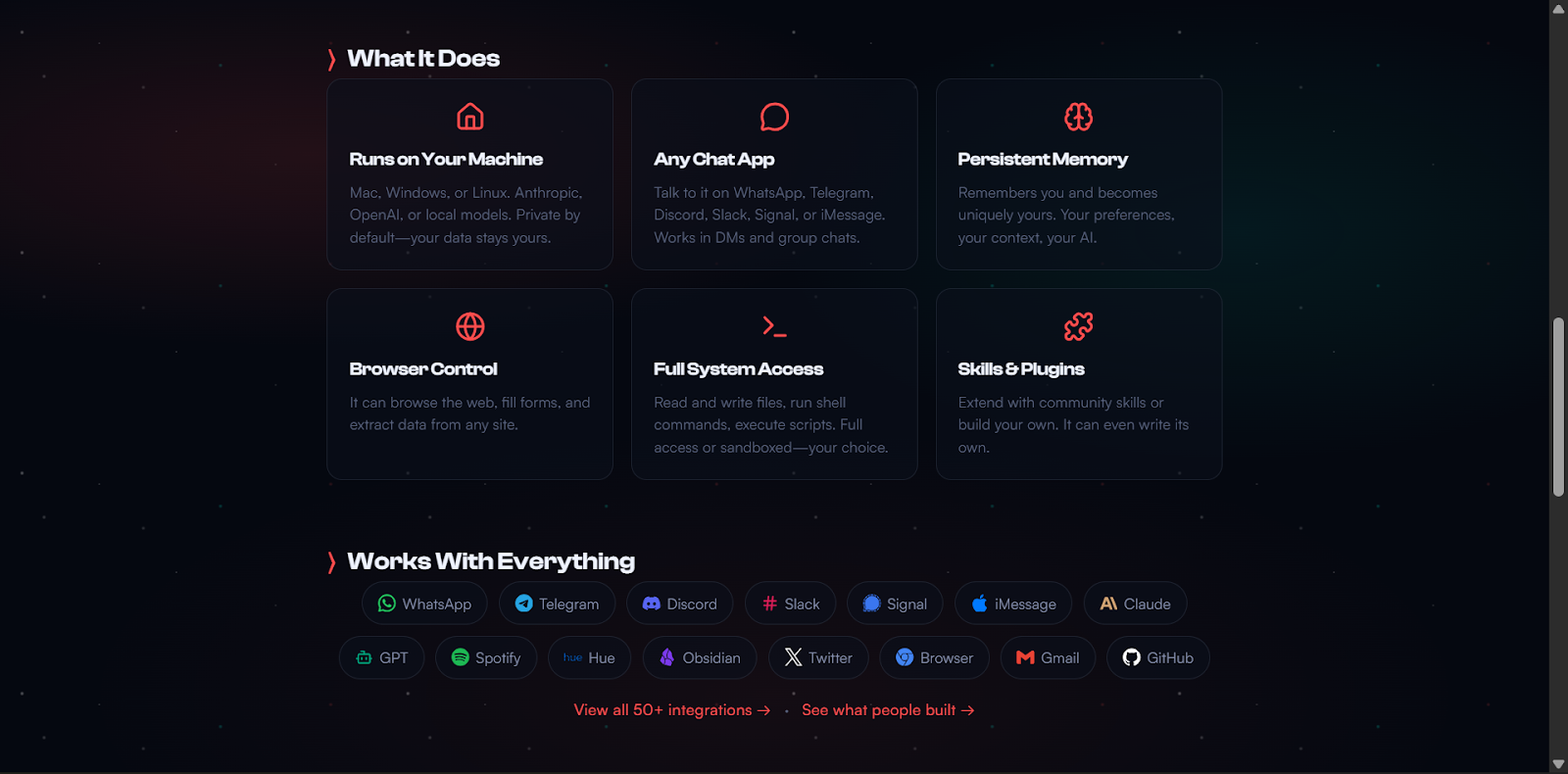
Zama Product Ecosystem
Zama Protocol: The foundation of the ecosystem, develops fully homomorphic encryption (FHE) for secure and private data processing.ZAMA Token: Powers the ecosystem by facilitating transactions, incentivizing developers, and supporting governance within the network.Developer Tools: A suite of open-source tools designed to help developers integrate FHE into their applications seamlessly.Enables confidential Smart Contracts: Enable the creation of decentralized applications (dApps) that maintain user privacy and data confidentiality.Zama Network: A robust infrastructure that supports encrypted computations and ensures scalability for real-world applications.Ecosystem Partnerships: Collaborations with industries like DeFi, AI, and healthcare to drive adoption and innovation.
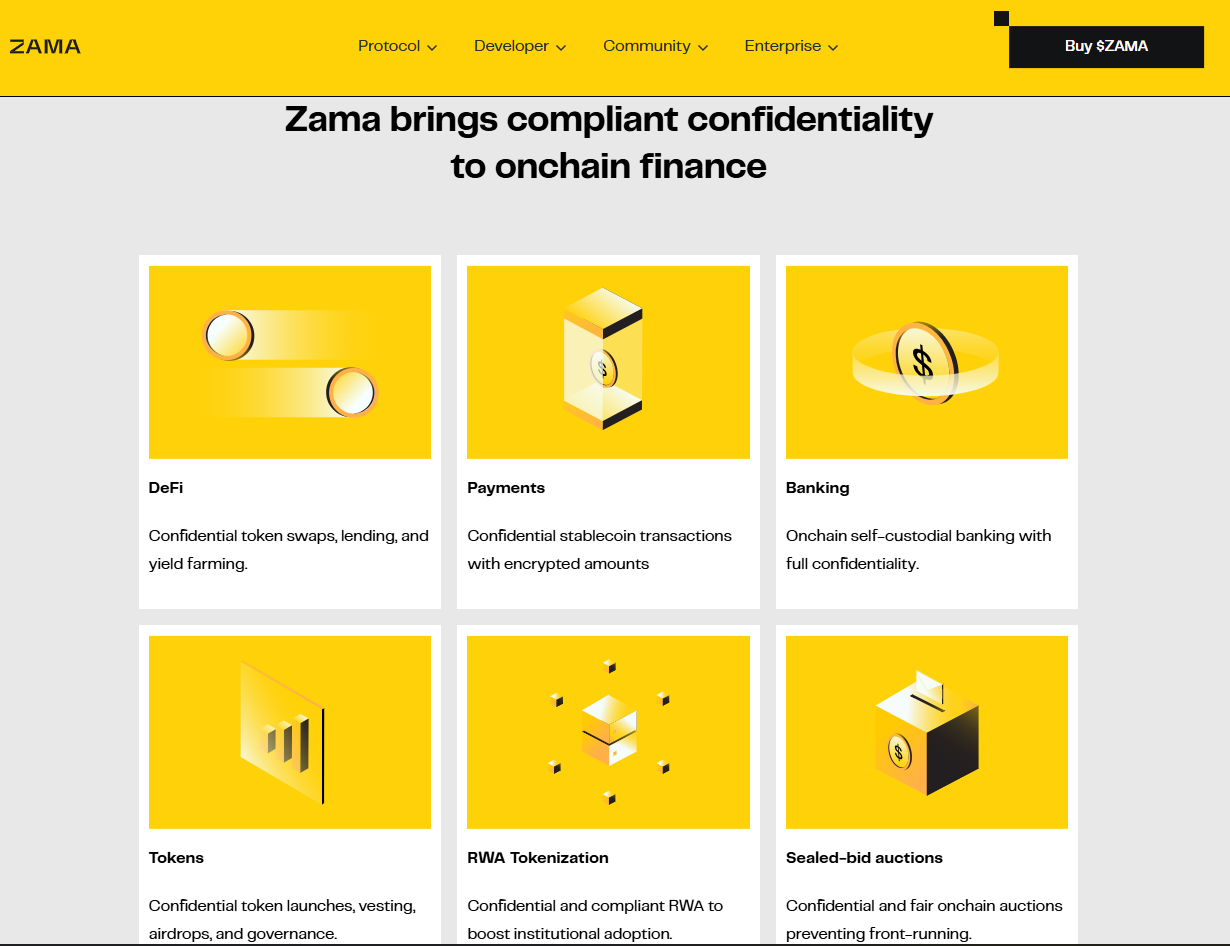
Zama Use Cases and Applications


As more on-chain activity involves real users, assets, and organizations, privacy becomes essential rather than optional. Zama’s technology enables applications that need a compliant confidentiality layer without giving up decentralization or auditability. The following are some of the most important use cases emerging across the Zama Network and the broader Zama ecosystem.
1. Confidential DeFi (Private Balances and Trades)
DeFi applications expose user balances, positions, and trading strategies by default. Zama’s technology allows protocols to hide balances and transaction details while still enforcing rules and settlement logic on-chain. Traders can protect sensitive information without relying on off-chain systems or trusted intermediaries.
2. Private Stablecoins and Payments
Stablecoins and payment systems often require privacy for everyday use and regulatory alignment. The Zama Network supports encrypted transfers and balances, enabling private payments that still allow compliance checks and controlled disclosures when required.
3. Privacy-Preserving AI
AI models depend on large volumes of sensitive data. Zama’s technology allows encrypted data to be processed directly, making it possible to run AI computations without exposing raw inputs. This approach helps protect user underlying data while supporting decentralized AI crypto workflows, making it central to many of the best AI crypto projects for decentralized applications.
4. RWA Tokenization
Tokenizing real-world assets often involves confidential financial and ownership data. The Zama ecosystem supports encrypted logic for asset management, valuation, and transfers, making on-chain representation of real-world assets more practical and secure.
5. Identity and Compliance Systems
Identity systems must balance privacy with verification. Zama’s technology enables encrypted identity attributes that can be checked without revealing underlying personal information. This design supports regulatory compliance while respecting user privacy.
6. Enterprise and Healthcare Data Processing
Enterprises and healthcare providers manage highly sensitive data that cannot be made public. The Zama Network allows encrypted internet data processing for analytics, billing, and record management, making blockchain viable for industries that require a strict confidentiality layer.
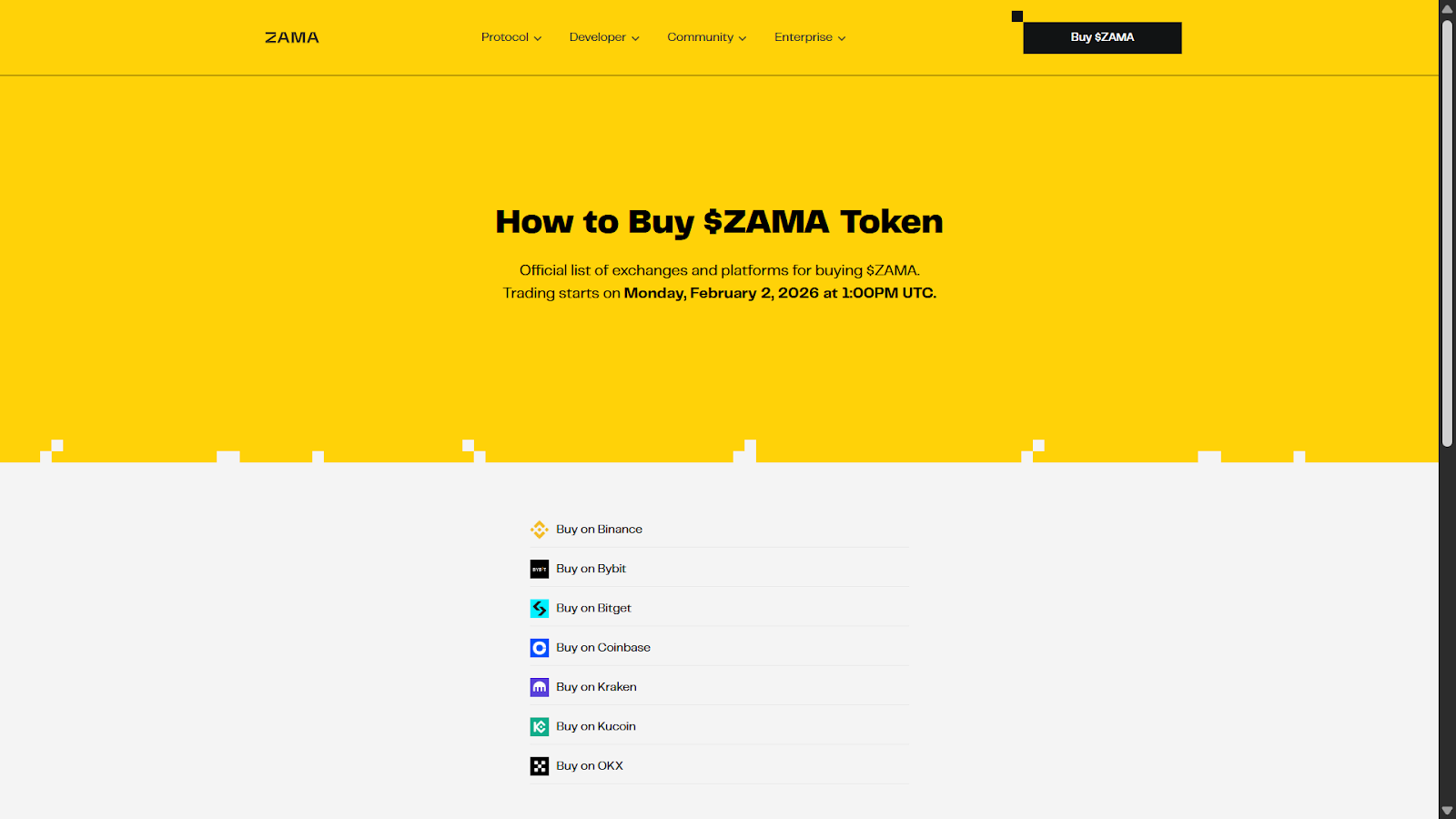
ZAMA Token Overview
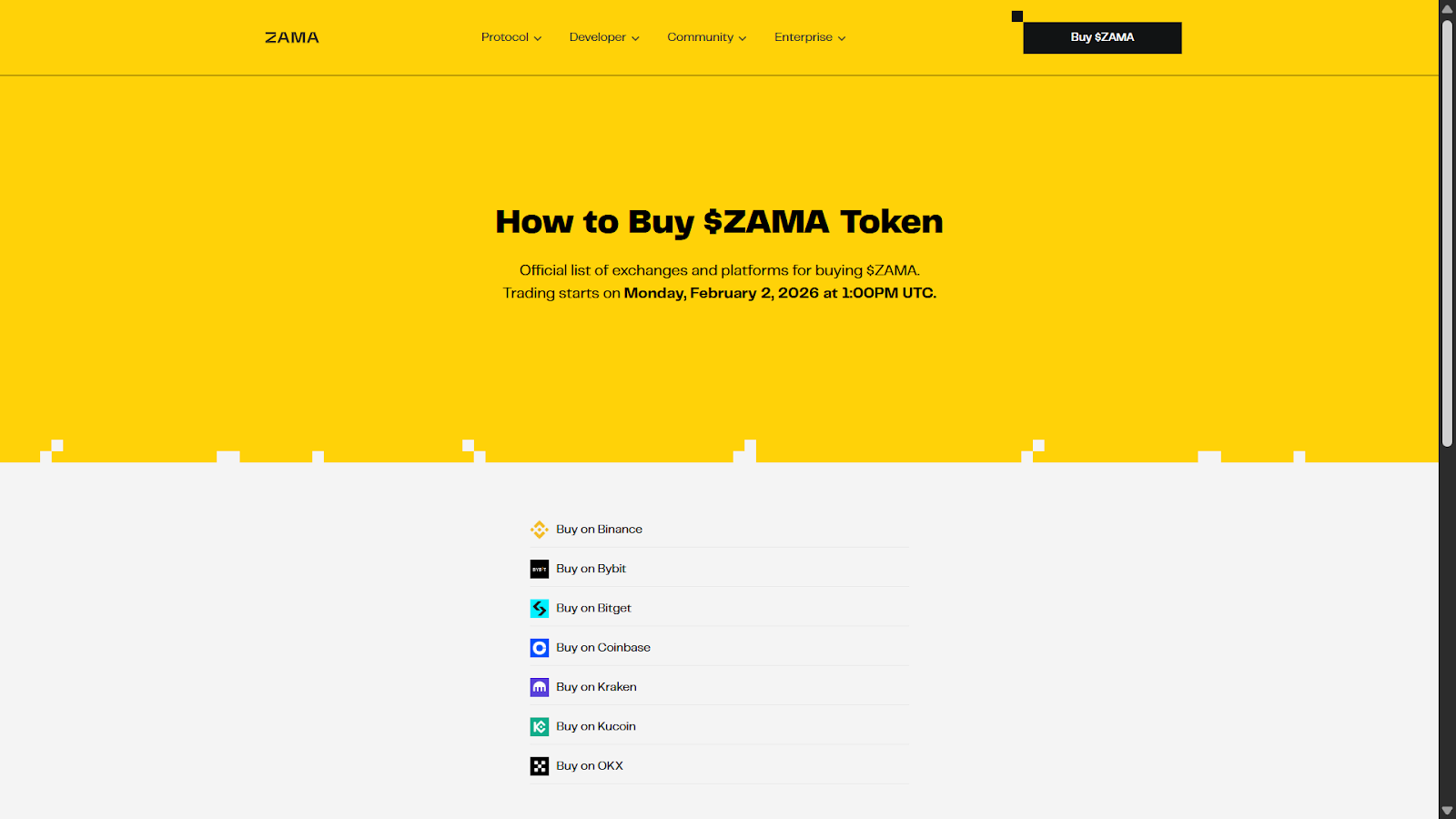
The ZAMA token plays a central role in supporting the privacy technologies in crypto that define Zama’s ecosystem. It serves as a key component in driving adoption, incentivizing participation, and ensuring the network’s sustainability. The following are the main aspects of the ZAMA token:
Token Utility
The ZAMA token powers the ecosystem by facilitating transactions, enabling governance, and incentivizing developers to build privacy-preserving applications. It ensures that participants can seamlessly interact within the Zama Network while maintaining data confidentiality.
Emissions and Incentives
Zama’s tokenomics include a well-structured emissions plan designed to reward early adopters and contributors. Incentives are distributed to developers, validators, and other participants who actively support the growth and security of the network.
Distribution Model
The token distribution model ensures a balanced allocation between stakeholders, including the community, developers, and investors. This approach promotes decentralization and long-term sustainability while fostering trust within the ecosystem.
Zama vs Other Privacy Technologies
Zama’s technology stands out in the realm of privacy-preserving decentralized applications, offering unique advantages over other privacy solutions. The following comparisons highlight how Zama differs from other leading technologies in terms of functionality, scalability, and security.
Zama vs Zero-Knowledge Proofs (ZKPs)
FeatureZamaZero-Knowledge Proofs (ZKPs)Data ProcessingProcesses encrypted data directlyVerifies data without revealing itScalabilityHigh scalability for complex computationsLimited scalability for large datasetsUse CasesBroader applications in AI, DeFi, and morePrimarily used for transaction privacy
Zama vs Secure Multi-Party Computation (MPC)
FeatureZamaSecure Multi-Party Computation (MPC)Data HandlingProcesses encrypted data independentlyRequires multiple parties to collaborateEfficiencyMore efficient for single-party confidential operationsHigher overhead due to multi-party setupApplicationsIdeal for privacy-preserving dAppsLimited to collaborative computations
Zama vs Trusted Execution Environments (TEE)
FeatureZamaTrusted Execution Environments (TEE)Security ModelRelies on encryption for privacyRelies on hardware-based securityFlexibilitySoftware-based, adaptable to various use casesHardware-dependent, less flexibleTrust RequirementsNo reliance on hardware manufacturersRequires trust in hardware providers
Zama Roadmap and Future Development
The Zama ecosystem is poised for significant growth, with a clear roadmap that focuses on advancing privacy-preserving technologies and expanding its applications. Upcoming developments include enhancements to the fully homomorphic encryption practical framework, making it even more efficient and scalable for real-world use cases. Plans to integrate with additional blockchain networks aim to broaden the reach of Zama’s technology, fostering adoption across diverse industries.
Efforts to strengthen developer tools and resources will empower the community to build innovative privacy-preserving decentralized applications. Strategic partnerships with key players in sectors like DeFi, AI, and healthcare are expected to drive further innovation and collaboration. The roadmap reflects Zama’s commitment to creating a robust and sustainable ecosystem that prioritizes data privacy and security while enabling transformative solutions.
Conclusion
Zama’s technology offers a groundbreaking approach to data privacy and security, making it a valuable solution for industries that handle sensitive information. Its fully homomorphic encryption practical, open-source framework, and versatile applications position it as a leader in privacy-preserving decentralized applications. The Zama ecosystem provides the tools and infrastructure needed to drive innovation while ensuring compliance and confidentiality. This combination of advanced technology and practical usability makes Zama an ideal choice for organizations seeking to adopt secure and scalable blockchain solutions.
FAQs
Is Zama a blockchain or a protocol?
Zama confidential blockchain protocol, not a standalone blockchain. It provides a fully homomorphic encryption (FHE) framework that can integrate with existing blockchain networks to enable privacy-preserving computations.
Does Zama have a native token?
Yes, Zama has a native token called the ZAMA token. It powers the Zama ecosystem by facilitating transactions, incentivizing developers, and supporting governance within the network.
What is Zama used for?
Zama is used for enabling privacy-preserving decentralized applications across various industries. Its applications include confidential DeFi, private stablecoins, privacy-preserving AI, RWA tokenization, identity systems, and secure enterprise data processing.
How is Zama different from ZK privacy projects?
Zama is different from ZK privacy projects because it uses fully homomorphic encryption (FHE) to process encrypted data directly, while ZK projects focus on verifying data without revealing it. This makes Zama more versatile for complex computations and broader use cases.